How to remove FinSpy from Mac?
Remove malware from Mac manually: The Activity Monitor. If you know which app on your Mac is. Back up, Format and Restore to Remove Spyware from Mac. In some instances, the damage is severe. This can be in cases where the spyware is deeply embedded in the system. In such a case, you format the Mac hard drive and reinstall the OS afresh. This method of removing spyware from Mac is costly hence should be considered as the last option.
What is FinSpy?
FinSpy is the name of spyware which can be used to log keystrokes, record audio via microphone and video via webcam, execute remote shell commands, extract system information and other data. Therefore, cyber criminals can use this spyware for the purposes of spying, stealing data and remotely controlling the infected computer.

Keystroke logging feature allows malicious programs like FinSpy to monitor keyboard input, in other words, to record data entered with the keyboard. In most cases cyber criminals use this feature to steal information such as login credentials (like usernames, email addresses, passwords) and credit card details. Such information could be misused to make fraudulent purchases, transactions, steal personal accounts, identities, and for other malicious purposes. Data enumeration feature allows user names, network resources, shares and services from a system, and other information that could be used to detect the vulnerabilities (or weak points) in the system security. Data exfiltration feature allows to transfer (collect) copied data to from the infected computer or server. Also, FinSpy can be used to execute various commands, for example, it may be used to restart, shut down a computer, or even download and execute various files that may be used to cause installation of some other malware. Additionally, this spyware allows cyber criminals to access victim's microphone, webcam and take screenshots. They could use recorded material to blackmail victims, for example, they may demand to be paid a certain amount of money for not publishing recorded material on some website or sending it to other people.
| Name | FinSpy malware |
| Threat Type | Spyware. |
| Detection Names | Avast (MacOS:Agent-KN [Trj]), AVG (MacOS:Agent-KN [Trj]), ESET-NOD32 (OSX/FinSpy.A), Kaspersky (HEUR:Trojan.OSX.Agent.gen), Full List (VirusTotal) |
| Symptoms | Spyware is designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, monetary loss, installation of some other malware |
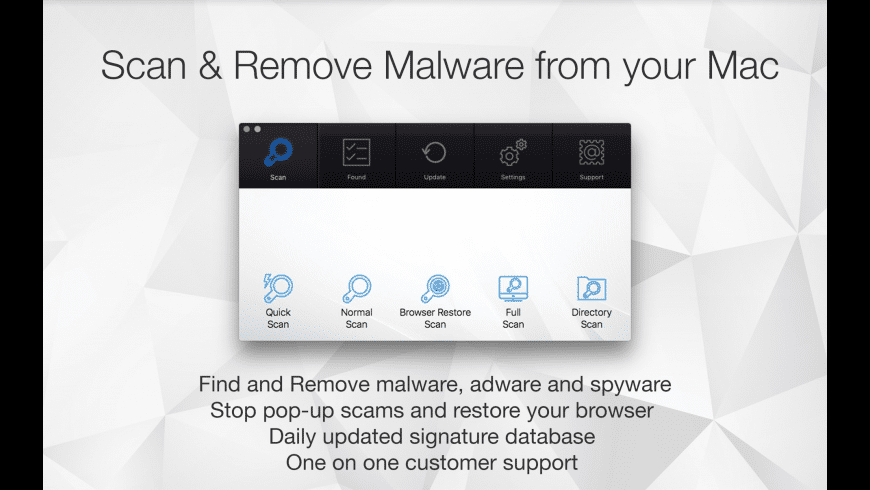
| Malware Removal (Mac) | To eliminate possible malware infections, scan your Mac with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
To sum up, users who would install FinSpy on the operating system could become victims of identity theft, suffer monetary loss, lose access to various personal accounts, have their computers infected with some other malware, experience serious issues related to online privacy, browsing safety, etc. A couple of examples of other malware targeting Mac computers are Eleanor, Proton and XCSSET.
How did malware install on my computer?
In most cases operating systems get infected with malicious software through malspam campaigns (emails), Trojans, fake software updating tools, unofficial activation ('cracking') tools and questionable file, software download sources. Cyber criminals attempt to proliferate malware via spam malcampaigns by sending emails with malicious attachments or website links designed to download malicious files in them. Usually they send emails that contain files like Microsoft Office, PDF documents, archive files like ZIP, RAR, executable files (like .exe), or JavaScript files. If opened/executed, those files install malware on the operating system. Fake software updating tools can be designed either to infect operating systems by installing malicious software instead of updates, fixes for the installed one, or by exploiting bugs, flaws of outdated software. Trojans are malicious programs that can be designed to install other programs of this kind. When a system is infected with a Trojan, then it is very likely that it will get infected with other malware as well. Peer-to-peer networks (like torrent clients, eMule), free file hosting, freeware download, unofficial websites, third party downloaders, and other similar software download sources can be used to proliferate malicious program too. It can be done by disguising malicious files as harmless, regular. When users download and open those files, they infect systems with one or another malicious software. Unofficial activation tools are programs that supposed to illegally activate licensed software for free (bypass its activation). Nevertheless, instead of activating installed software those tools often install some malicious one.
How to avoid installation of malware?
Files and programs should be downloaded from official websites and via direct links. Other channels, sources that are mentioned in the paragraph above can be used to distribute malware. Therefore, they should not be used. The same applies to third party installers. Attachments and websites links in irrelevant emails that are received from unknown, suspicious addresses should not be opened. It is common that recipients who open files downloaded via such emails cause installation of malware. Furthermore, installed programs and operating system must be updated with tools and/or implemented functions that are provided (designed) by their official software developers. Third party, unofficial tools should never be used for that, also, it is not legal to activate licensed programs with such tools. Additionally, operating system should be regularly scanned for threats with a reputable antivirus or anti-spyware software. It is important to keep such software up to date. If your computer is already infected with PUAs, we recommend running a scan with Combo Cleaner Antivirus for macOS to automatically eliminate them.
Pop-up window which appears after execution of a malicious executable designed to install FinSpy:
Instant automatic Mac malware removal:Manual threat removal might be a lengthy and complicated process that requires advanced computer skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of Mac malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner for MacBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited three days free trial available.
Quick menu:
- STEP 1. Remove malware related files and folders from OSX.
- STEP 2. Remove rogue extensions from Safari.
- STEP 3. Remove rogue add-ons from Google Chrome.
- STEP 4. Remove potentially unwanted plug-ins from Mozilla Firefox.
Video showing how to remove adware and browser hijackers from a Mac computer:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your 'Applications' folder:
Click the Finder icon. In the Finder window, select 'Applications'. In the applications folder, look for 'MPlayerX', 'NicePlayer', or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited three days free trial available.
Remove finspy malware related files and folders:
Click the Finder icon, from the menu bar. Choose Go, and click Go to Folder...
Check for adware-generated files in the /Library/LaunchAgents folder:
In the Go to Folder... bar, type: /Library/LaunchAgents
In the 'LaunchAgents' folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - 'installmac.AppRemoval.plist', 'myppes.download.plist', 'mykotlerino.ltvbit.plist', 'kuklorest.update.plist', etc. Adware commonly installs several files with the same string.
Check for adware generated files in the /Library/Application Support folder:
In the Go to Folder... bar, type: /Library/Application Support
In the 'Application Support' folder, look for any recently-added suspicious folders. For example, 'MplayerX' or 'NicePlayer', and move these folders to the Trash.
Check for adware-generated files in the ~/Library/LaunchAgents folder:
In the Go to Folder bar, type: ~/Library/LaunchAgents
In the 'LaunchAgents' folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - 'installmac.AppRemoval.plist', 'myppes.download.plist', 'mykotlerino.ltvbit.plist', 'kuklorest.update.plist', etc. Adware commonly installs several files with the same string.
Check for adware-generated files in the /Library/LaunchDaemons folder:
In the Go to Folder... bar, type: /Library/LaunchDaemons
In the 'LaunchDaemons' folder, look for recently-added suspicious files. For example 'com.aoudad.net-preferences.plist', 'com.myppes.net-preferences.plist', 'com.kuklorest.net-preferences.plist', 'com.avickUpd.plist', etc., and move them to the Trash.
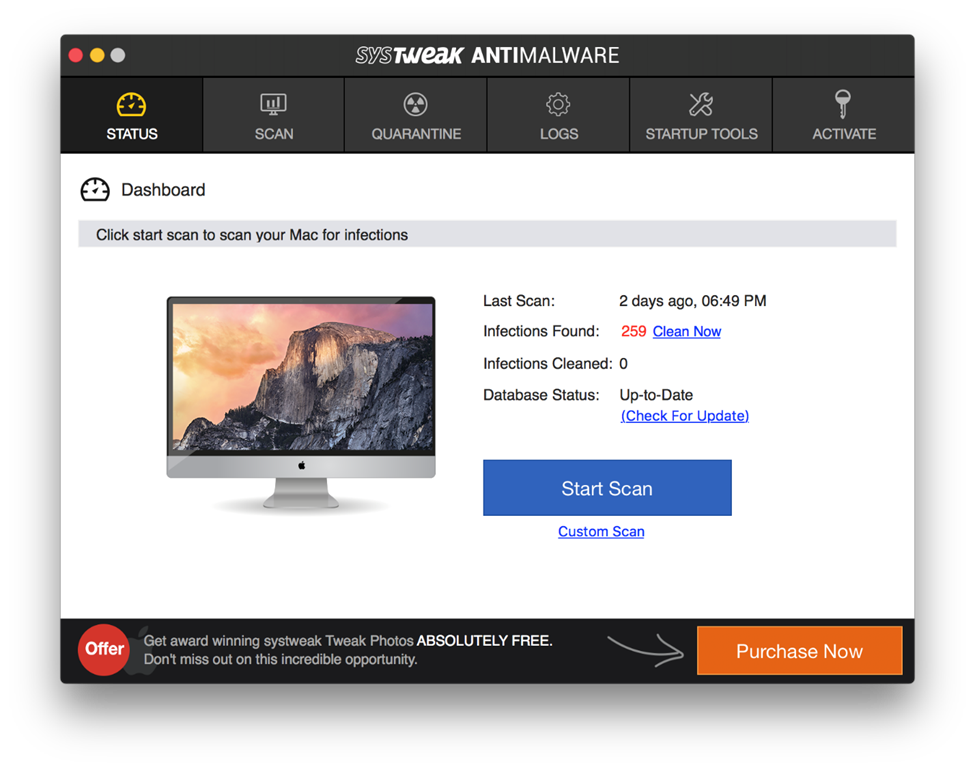
Scan your Mac with Combo Cleaner:
If you have followed all the steps in the correct order you Mac should be clean of infections. To be sure your system is not infected run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file double click combocleaner.dmg installer, in the opened window drag and drop Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates it's virus definition database and click 'Start Combo Scan' button.
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays 'no threats found' - this means that you can continue with the removal guide, otherwise it's recommended to remove any found infections before continuing.
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
FinSpy malware removal from Internet browsers:
Remove malicious extensions from Safari:
Remove finspy malware related Safari extensions:
Open Safari browser, from the menu bar, select 'Safari' and click 'Preferences...'.
In the preferences window, select 'Extensions' and look for any recently-installed suspicious extensions. When located, click the 'Uninstall' button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for normal browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
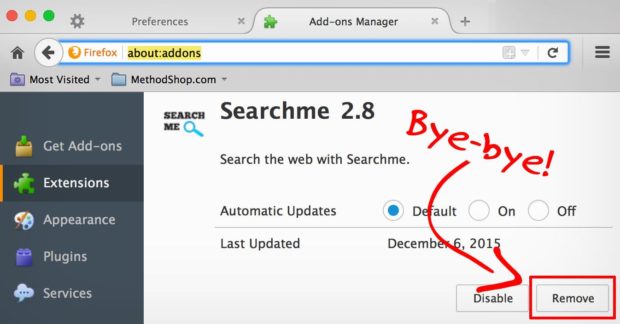
Remove malicious plug-ins from Mozilla Firefox:
Remove finspy malware related Mozilla Firefox add-ons:
Open your Mozilla Firefox browser. At the top right corner of the screen, click the 'Open Menu' (three horizontal lines) button. From the opened menu, choose 'Add-ons'.
Choose the 'Extensions' tab and look for any recently-installed suspicious add-ons. When located, click the 'Remove' button next to it/them. Note that you can safely uninstall all extensions from your Mozilla Firefox browser - none are crucial for normal browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Mozilla Firefox.
Free Spyware Removal For Mac Os X
Remove malicious extensions from Google Chrome:
Remove finspy malware related Google Chrome add-ons:

Keystroke logging feature allows malicious programs like FinSpy to monitor keyboard input, in other words, to record data entered with the keyboard. In most cases cyber criminals use this feature to steal information such as login credentials (like usernames, email addresses, passwords) and credit card details. Such information could be misused to make fraudulent purchases, transactions, steal personal accounts, identities, and for other malicious purposes. Data enumeration feature allows user names, network resources, shares and services from a system, and other information that could be used to detect the vulnerabilities (or weak points) in the system security. Data exfiltration feature allows to transfer (collect) copied data to from the infected computer or server. Also, FinSpy can be used to execute various commands, for example, it may be used to restart, shut down a computer, or even download and execute various files that may be used to cause installation of some other malware. Additionally, this spyware allows cyber criminals to access victim's microphone, webcam and take screenshots. They could use recorded material to blackmail victims, for example, they may demand to be paid a certain amount of money for not publishing recorded material on some website or sending it to other people.
| Name | FinSpy malware |
| Threat Type | Spyware. |
| Detection Names | Avast (MacOS:Agent-KN [Trj]), AVG (MacOS:Agent-KN [Trj]), ESET-NOD32 (OSX/FinSpy.A), Kaspersky (HEUR:Trojan.OSX.Agent.gen), Full List (VirusTotal) |
| Symptoms | Spyware is designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, monetary loss, installation of some other malware |
| Malware Removal (Mac) | To eliminate possible malware infections, scan your Mac with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
To sum up, users who would install FinSpy on the operating system could become victims of identity theft, suffer monetary loss, lose access to various personal accounts, have their computers infected with some other malware, experience serious issues related to online privacy, browsing safety, etc. A couple of examples of other malware targeting Mac computers are Eleanor, Proton and XCSSET.
How did malware install on my computer?
In most cases operating systems get infected with malicious software through malspam campaigns (emails), Trojans, fake software updating tools, unofficial activation ('cracking') tools and questionable file, software download sources. Cyber criminals attempt to proliferate malware via spam malcampaigns by sending emails with malicious attachments or website links designed to download malicious files in them. Usually they send emails that contain files like Microsoft Office, PDF documents, archive files like ZIP, RAR, executable files (like .exe), or JavaScript files. If opened/executed, those files install malware on the operating system. Fake software updating tools can be designed either to infect operating systems by installing malicious software instead of updates, fixes for the installed one, or by exploiting bugs, flaws of outdated software. Trojans are malicious programs that can be designed to install other programs of this kind. When a system is infected with a Trojan, then it is very likely that it will get infected with other malware as well. Peer-to-peer networks (like torrent clients, eMule), free file hosting, freeware download, unofficial websites, third party downloaders, and other similar software download sources can be used to proliferate malicious program too. It can be done by disguising malicious files as harmless, regular. When users download and open those files, they infect systems with one or another malicious software. Unofficial activation tools are programs that supposed to illegally activate licensed software for free (bypass its activation). Nevertheless, instead of activating installed software those tools often install some malicious one.
How to avoid installation of malware?
Files and programs should be downloaded from official websites and via direct links. Other channels, sources that are mentioned in the paragraph above can be used to distribute malware. Therefore, they should not be used. The same applies to third party installers. Attachments and websites links in irrelevant emails that are received from unknown, suspicious addresses should not be opened. It is common that recipients who open files downloaded via such emails cause installation of malware. Furthermore, installed programs and operating system must be updated with tools and/or implemented functions that are provided (designed) by their official software developers. Third party, unofficial tools should never be used for that, also, it is not legal to activate licensed programs with such tools. Additionally, operating system should be regularly scanned for threats with a reputable antivirus or anti-spyware software. It is important to keep such software up to date. If your computer is already infected with PUAs, we recommend running a scan with Combo Cleaner Antivirus for macOS to automatically eliminate them.
Pop-up window which appears after execution of a malicious executable designed to install FinSpy:
Instant automatic Mac malware removal:Manual threat removal might be a lengthy and complicated process that requires advanced computer skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of Mac malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner for MacBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited three days free trial available.
Quick menu:
- STEP 1. Remove malware related files and folders from OSX.
- STEP 2. Remove rogue extensions from Safari.
- STEP 3. Remove rogue add-ons from Google Chrome.
- STEP 4. Remove potentially unwanted plug-ins from Mozilla Firefox.
Video showing how to remove adware and browser hijackers from a Mac computer:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your 'Applications' folder:
Click the Finder icon. In the Finder window, select 'Applications'. In the applications folder, look for 'MPlayerX', 'NicePlayer', or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited three days free trial available.
Remove finspy malware related files and folders:
Click the Finder icon, from the menu bar. Choose Go, and click Go to Folder...
Check for adware-generated files in the /Library/LaunchAgents folder:
In the Go to Folder... bar, type: /Library/LaunchAgents
In the 'LaunchAgents' folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - 'installmac.AppRemoval.plist', 'myppes.download.plist', 'mykotlerino.ltvbit.plist', 'kuklorest.update.plist', etc. Adware commonly installs several files with the same string.
Check for adware generated files in the /Library/Application Support folder:
In the Go to Folder... bar, type: /Library/Application Support
In the 'Application Support' folder, look for any recently-added suspicious folders. For example, 'MplayerX' or 'NicePlayer', and move these folders to the Trash.
Check for adware-generated files in the ~/Library/LaunchAgents folder:
In the Go to Folder bar, type: ~/Library/LaunchAgents
In the 'LaunchAgents' folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - 'installmac.AppRemoval.plist', 'myppes.download.plist', 'mykotlerino.ltvbit.plist', 'kuklorest.update.plist', etc. Adware commonly installs several files with the same string.
Check for adware-generated files in the /Library/LaunchDaemons folder:
In the Go to Folder... bar, type: /Library/LaunchDaemons
In the 'LaunchDaemons' folder, look for recently-added suspicious files. For example 'com.aoudad.net-preferences.plist', 'com.myppes.net-preferences.plist', 'com.kuklorest.net-preferences.plist', 'com.avickUpd.plist', etc., and move them to the Trash.
Scan your Mac with Combo Cleaner:
If you have followed all the steps in the correct order you Mac should be clean of infections. To be sure your system is not infected run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file double click combocleaner.dmg installer, in the opened window drag and drop Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates it's virus definition database and click 'Start Combo Scan' button.
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays 'no threats found' - this means that you can continue with the removal guide, otherwise it's recommended to remove any found infections before continuing.
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
FinSpy malware removal from Internet browsers:
Remove malicious extensions from Safari:
Remove finspy malware related Safari extensions:
Open Safari browser, from the menu bar, select 'Safari' and click 'Preferences...'.
In the preferences window, select 'Extensions' and look for any recently-installed suspicious extensions. When located, click the 'Uninstall' button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for normal browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
Remove malicious plug-ins from Mozilla Firefox:
Remove finspy malware related Mozilla Firefox add-ons:
Open your Mozilla Firefox browser. At the top right corner of the screen, click the 'Open Menu' (three horizontal lines) button. From the opened menu, choose 'Add-ons'.
Choose the 'Extensions' tab and look for any recently-installed suspicious add-ons. When located, click the 'Remove' button next to it/them. Note that you can safely uninstall all extensions from your Mozilla Firefox browser - none are crucial for normal browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Mozilla Firefox.
Free Spyware Removal For Mac Os X
Remove malicious extensions from Google Chrome:
Remove finspy malware related Google Chrome add-ons:
Open Google Chrome and click the 'Chrome menu' (three horizontal lines) button located in the top-right corner of the browser window. From the drop-down menu, choose 'More Tools' and select 'Extensions'.
Remove Spyware Malware Mac
In the 'Extensions' window, look for any recently-installed suspicious add-ons. When located, click the 'Trash' button next to it/them. Note that you can safely uninstall all extensions from your Google Chrome browser - none are crucial for normal browser operation.
Free Spyware Removal Microsoft
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.

